Sets of Android apps installed on the same smartphone have ways for plotting to extract information about the phone’s user. Which can be hard to recognize and easy for data leak. Security specialists don’t have much difficulty making sense of if a single app is get-together sensitive information and secretly sending it off to a server someplace. In any case, when two apps collaborate, neither may hint at conclusive robbery alone. What’s more, due to a huge number of conceivable app blends, testing for application collisions is a huge task.
Table of Contents
What research said about data leak?

A research release for the current week built up another approach to handling this issue and discovered more than 20k application pairings that data leak. Four specialists at Virginia Tech made a framework that digs into the architecture of Android applications to see how they trade data with different applications on a similar phone. Their framework DIALDroid then couples apps to test how they’d connect. And whether they could conceivably cooperate to release sensitive data.
At the point when the analysts set DIALDroid loose on the 1 lakh most downloaded Android apps. They turned up almost 23k apps matches that leaked data. More than 16k of those sets likewise included benefit heightening. Which implies the second app got a sort of sensitive data that it’s commonly forbidden from getting to.
How can data leak from apps?

Generally, small groups of unsecured applications were behind the enormous number of defective connection. The 16k application matches that displayed benefit heightening all included one of 33 sender applications. What’s more, the approximately 6k application combines that leaked data without benefit acceleration all included one of 21 sender applications. Twenty sender applications showed up in both classes. The risky applications came in different structures: from amusement and games to photography and transportation applications.
Sometimes just a single app in a matching may appear to be intentionally malicious. An app can exploit a security defect in another app to take information and concentrate it to a far off server, for example. Different circumstances, both apps are ineffectively designed, making a coincidental data flow out of one app to another and after that from the second to a log document.
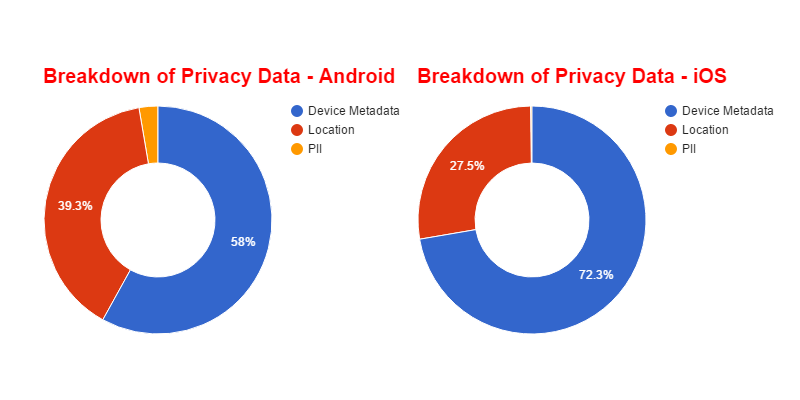
The research found that smartphone location will probably be spilled than some other kind of data. It’s simpler to imagine how a user’s constant location could be abused than, say, what networks that individual’s smartphone is connected with. In any case, littler points of interest like network state can be utilized to “unique mark” a gadget—that is, to distinguish it and monitor what its user do after some time.
“For the most time, logged data is just accessible to the app that made it. However, some cyber attacks can remove information from log records, which implies the leak data could any case be risky. Other all the more quickly unsafe app pairings send information far from the smartphone over the web, or even over SMS. Sixteen sender apps and 32 recipient apps utilized permission heightening and separated leaked data in one of those two ways.”